Huawei B593 Driver Firmware Download 2016 Word
Has launched a upgraded version router of, calls it B315. It comes in black and white color, looks beautiful in design. It is listed in the company website, but there is no word on price.
HUAWEI - the global leader in telecoms with a great range of products including mobile phones, tablets, wearables, PCs, broadband devices and home devices.
Its submodel devices are available as B315S-936 (Globe Philippines), B315s-607 and B315s-22. The device can be purchased in market for about US $300. The B315 is a 4G LTE router where B315s-607 supports FDD 700/900/1800/2100/2600 & TDD 2300Mhz and B315s-22 features FDD 800/900/1800/2100/2600 & TDD 2600Mhz operating frequency bands. Comparing to its previous model B593, B315 has faster wireless performance and it has a complete suite of Voice over IP (VOIP) functions which were not present in B593. The B315s Huawei gateway lets you connect to LTE network with speed up to 150 Mbps.
At the back of B315 router, there are 4 Ethernet ports for LAN/WAN and 1 telephone port are available. It also comes with a USB 2.0 port which lets you can connect a printer or external memory for easy storage and transfer files between devices, such as HDD, flash drives, network storage devices and printers. This CPE could cover smoother wireless network for 250 meters.
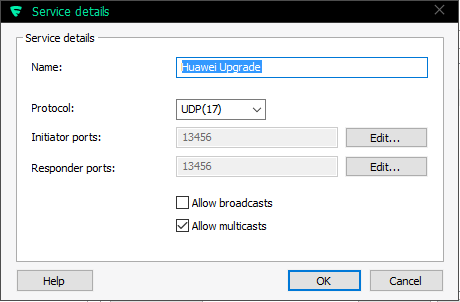
I finally cracked this! Just to clarify, I'm running an u-12 model with the. Using the ping-exploit to loosen firewall rules The first thing to is open the firewall to allow local access to the box. Ubratj okno master aktivacii microsoft office. In my I already established, that all the good ports are blocked by IPtables in the Linux. So, the previously published (I'm doing this on my Linux PC):./B593cmd.pl -the-IP- -the-admin-Pwd- 'iptables -I INPUT -i br0 -j ACCEPT' Now all ports are open from the LAN, but there are no changes to the Internet side.
We confirm this by running nmap: Nmap scan report for -the-IP- Host is up (0.0082s latency). Not shown: 993 closed ports PORT STATE SERVICE 21/tcp open ftp 22/tcp open ssh 23/tcp open telnet 80/tcp open http 443/tcp open https 631/tcp open ipp 8081/tcp open blackice-icecap MAC Address: F8:3D:FF:F8:3D:FF (Huawei Technologies Co.) That is something that I have been able to do earlier, but could not gain anything concrete out of it. Confirm that you know the CLI-password Now that we can run any commands to the box, let's confirm the configuration:./B593cmd.pl -the-IP- -the-admin-Pwd- 'cat /var/curcfg.xml' less The output is a very long XML-file. The good parts are: The output clearly says, that web-GUI and telnet/SSH command line interface have separate user accounts for them. However, the passwords are encrypted.
I have been able to determine, that it is a BASE64-encoded string and the binary format increases in 64-bit blocks. The only conclusion is to assume, that the passwords are encrypted with a, but the encryption key, and possible initialization vector are currently unknown. Luckily I know what f5338SA1kb4= and 2n+mVpCOAaY= stand for. They are the default passwords to the box anyway and the manual says that default admin password is admin and default user password is user.
Logical, huh? If you don't know the password for CLI- admin, there is no way that you're getting in. Trying out the SSH Now, what can we do with the fact, that SSH is now open and we know the password for privileged admin-user? A SSH-login, when using the correct CLI-password will yield: # ssh admin@ -the-IP- admin@ -the-IP-'s password: Write failed: Broken pipe Not cool.
In my exploit-tool -article, I referred to Mr. Ronkainen's work at.
He said to execute a specific command via SSH. My next attempt is to follow his instruction: # ssh admin@ -the-IP- /bin/sh admin@ -the-IP-'s password: ------------------------------- -----Welcome to ATP Cli------ ------------------------------- ATP> WHOOO!! Now the hidden shell-command will work: ------------------------------- -----Welcome to ATP Cli------ ------------------------------- ATP>shell shell BusyBox vv1.9.1 (2012-11-20 16:01:41 CST) built-in shell (ash) Enter 'help' for a list of built-in commands. SSH with non-privileged user / Telnet To test this further, I attempted to login with user user. The non-privileged user does not have the hidden shell-command available and no access will be granted: # ssh user@ -the-IP- /bin/sh user@ -the-IP-'s password: ------------------------------- -----Welcome to ATP Cli------ ------------------------------- ATP>shell shell Command failed.